Dieser Artikel wurde ursprünglich auf Englisch veröffentlicht.
Warum digitale Souveränität 2026 auf die Agenda gehört
Erfahren Sie, was digitale Souveränität ist, und lernen Sie, wie Sie die Kontrolle über Ihre Daten, Systeme und Infrastruktur zurückgewinnen, um Risiken zu senken und Compliance sicherzustellen.


Inhaltsverzeichnis
Digitale Souveränität ist die Fähigkeit, Ihr digitales Umfeld zu kontrollieren, einschließlich Ihrer Daten, Ihrer Systeme und Ihrer Governance-Rahmenwerke.
Im Jahr 2026 steht diese Kontrolle unter enormem Druck. Vor allem, weil sich die digitale Infrastruktur zunehmend in den Händen weniger globaler Anbieter konzentriert.
Tatsächlich kontrollieren US-Hyperscaler heute mehr als 70 % des Cloud-Markts der Europäischen Union. Das weckt Sorgen über Abhängigkeit, Jurisdiktion und langfristige Resilienz.
Digitale Souveränität soll diese Abhängigkeit verringern. Sie hilft Ihnen, die Kontrolle zurückzugewinnen in einer Landschaft, in der Regeln, Zugriffe und Risiken nicht immer von Ihnen definiert werden.
Um zu verstehen, warum das für Enterprise-IT wichtig ist und wie der Weg zu einem souveräneren Setup aussieht, erklärt dieser Leitfaden die wichtigsten Konzepte, Risiken und praktischen Schritte.
Wichtige Erkenntnisse
Digitale Souveränität bedeutet Kontrolle über Ihr digitales Umfeld
Sie gibt Ihnen die Hoheit über Ihre Daten, Systeme und deren Governance, ohne vollständige Unabhängigkeit von globalen Anbietern zu verlangen.Sie geht über Datensouveränität hinaus
Datensouveränität konzentriert sich auf Daten. Digitale Souveränität umfasst dagegen Infrastruktur, Betrieb und rechtliche Kontrolle über Ihren gesamten Stack.Steigende Risiken machen sie zur geschäftlichen Priorität
Regulatorischer Druck, Vendor-Lock-in und geopolitische Spannungen erhöhen den Bedarf an Kontrolle, Resilienz und Compliance.Sie bringt messbare geschäftliche Vorteile
Digitale Souveränität verbessert die Resilienz, vereinfacht Compliance, ermöglicht Innovation und stärkt das Vertrauen der Stakeholder.Beginnen Sie dort, wo Kontrolle am wichtigsten ist
Arbeitsplattformen sind ein praxisnaher Einstieg. Lösungen wie sovara helfen Ihnen, die Kontrolle über Workflows, Daten und die Systementwicklung zurückzugewinnen, ohne Flexibilität zu verlieren.
Was ist digitale Souveränität? Zentrale Konzepte und Dimensionen
Digitale Souveränität ist die Kontrolle darüber, wie Ihre digitalen Systeme funktionieren, einschließlich ihres Standorts, ihrer Steuerung und der anwendbaren Gesetze.
Dafür müssen Sie keine vollständige Unabhängigkeit anstreben oder den Kontakt zu globalen Anbietern abbrechen.
Es geht ausschließlich darum, die Entscheidungsgewalt zu behalten, damit Sie wissen, wovon Sie abhängig sind, die Abwägungen verstehen und nicht in Systeme geraten, die Sie nicht kontrollieren können.
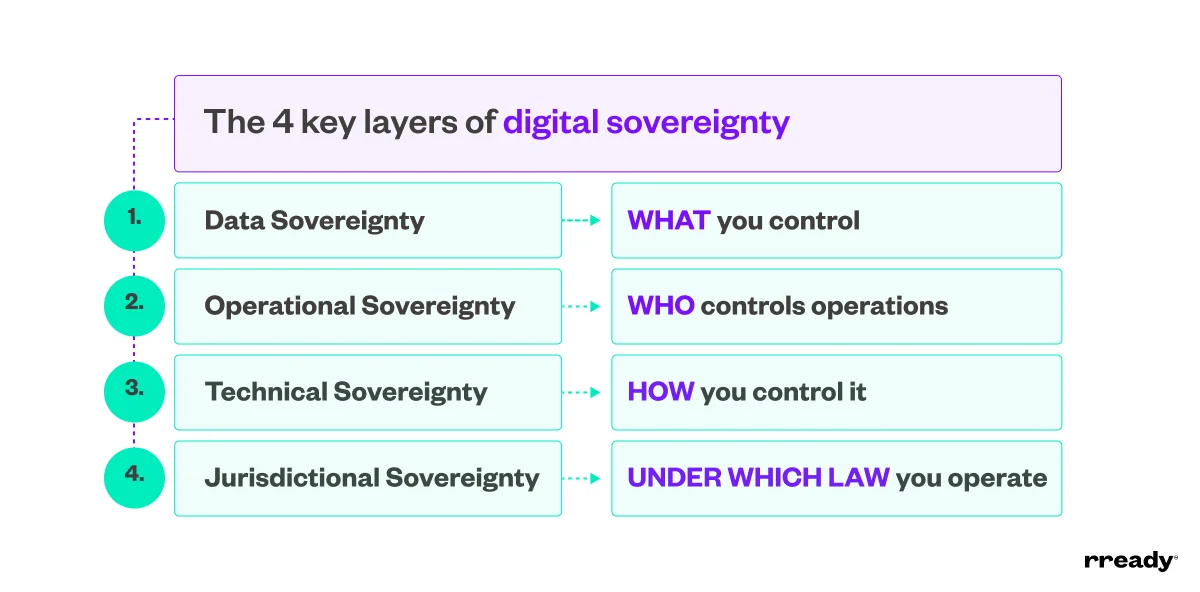
Was sind die Säulen digitaler Souveränität?
Digitale Souveränität basiert auf mehreren Kernsäulen, die definieren, wo Kontrolle besteht und wie sie in der Praxis durchgesetzt werden kann:
Datensouveränität: Daten bleiben unter Ihrer Kontrolle. Sie legen fest, wo sie gespeichert sind, wie sie gespeichert und verarbeitet werden, wer darauf zugreifen darf und wie sie übertragen oder gelöscht werden.
Operative Souveränität: Organisationen behalten die Kontrolle darüber, wer Systeme betreibt und wartet. So können kritische Workflows weiterlaufen, ohne auf externe Anbieter angewiesen zu sein.
Technische Souveränität: Systeme werden mit offener Architektur und Kontrollmechanismen gestaltet. So können Sie Ihre Technologie integrieren, anpassen und weiterentwickeln, ohne festgelegt zu sein.
Jurisdiktionale Souveränität: Ihr digitales Umfeld arbeitet unter den von Ihnen gewählten rechtlichen Rahmenbedingungen, mit Schutz vor externer rechtlicher Zugriffsgewalt oder widersprüchlichen Regeln.
Wer sollte über digitale Souveränität nachdenken?
Alle, die auf digitale Systeme angewiesen sind, sollten über digitale Souveränität nachdenken, darunter:
Regierungen und öffentliche Institutionen: Regierungen nutzen digitale Souveränität, um die Kontrolle über nationale Infrastrukturen zu behalten, Vorschriften durchzusetzen und die Kontinuität sowie Sicherheit öffentlicher Dienste zu gewährleisten.
Organisationen und Unternehmen: Organisationen sind betroffen durch ihre Abhängigkeit von Hardware, Software, Cloud-Diensten und externen Anbietern. Diese bestimmen, wie viel Kontrolle sie über Daten, Abläufe und Risikoexposition behalten.
Regulierte Branchen: Sektoren wie Gesundheitswesen, Finanzwesen, Energie und Telekommunikation brauchen digitale Souveränität, um strenge Compliance-Anforderungen zu erfüllen und zugleich kritische Daten und Infrastrukturen zu schützen.
Multinationale Unternehmen: Globale Organisationen nutzen Souveränitätsrahmen, um zentrale Systeme mit lokalen Vorschriften in Einklang zu bringen. So sichern sie Konsistenz, ohne die Compliance über Jurisdiktionen hinweg zu verlieren.
Privatpersonen: Privatpersonen nutzen digitale Souveränität, um ihre persönlichen Daten zu kontrollieren, ihre digitale Identität zu verwalten und zu schützen, wie ihre Informationen erhoben, verarbeitet und geteilt werden.
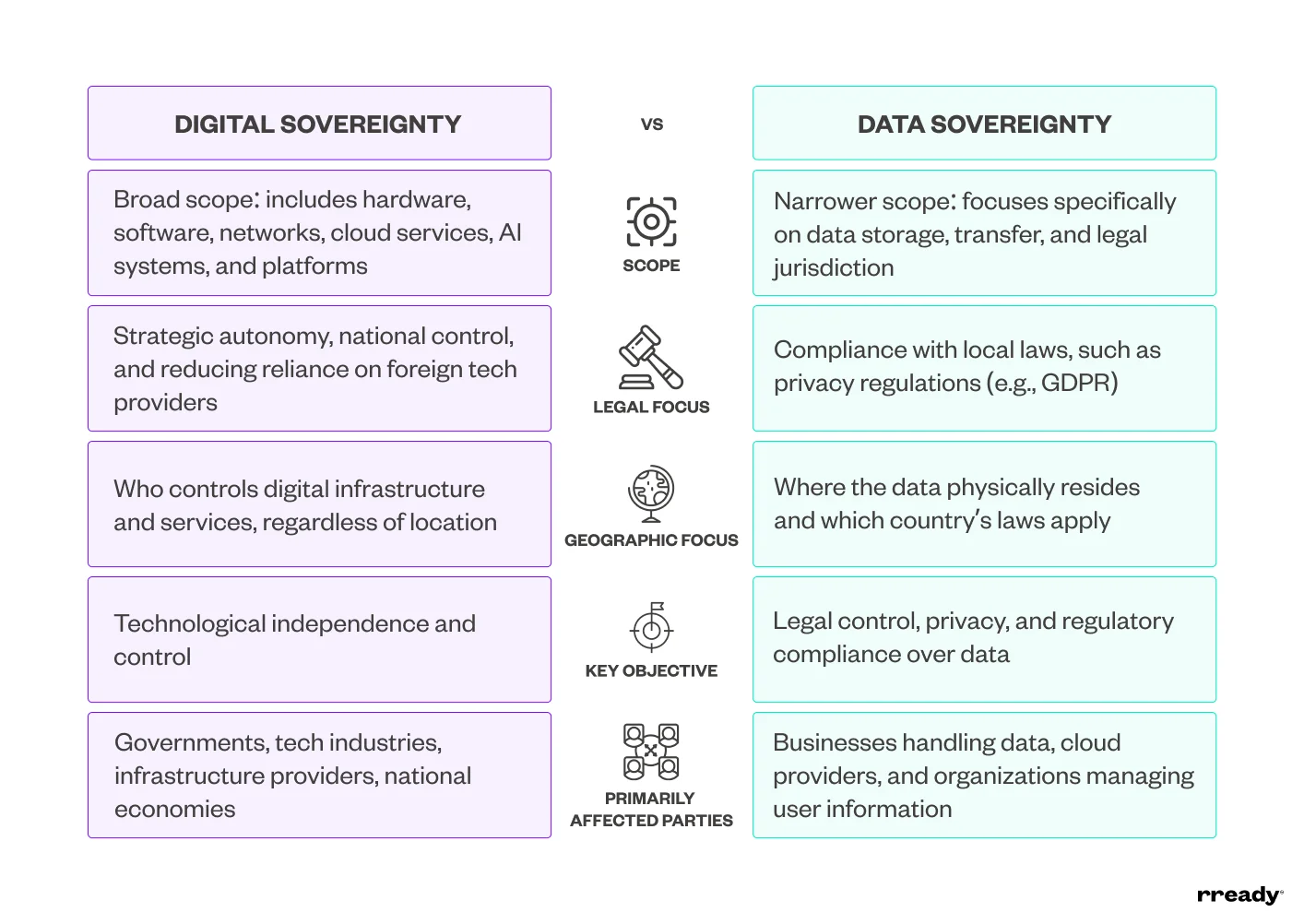
Was ist der Unterschied zwischen Datensouveränität und digitaler Souveränität?
Der Hauptunterschied zwischen Datensouveränität und digitaler Souveränität liegt im Umfang.
Datensouveränität konzentriert sich auf Daten und betrifft deren Speicherung, Verarbeitung und rechtliche Governance.
Digitale Souveränität geht weiter und umfasst auch die Systeme, die diese Daten verarbeiten, also Infrastruktur, Software, Betrieb und die Regeln, die sie steuern.
Einfach gesagt ist Datensouveränität ein Teil digitaler Souveränität, kein eigenständiges Konzept.
Warum digitale Souveränität jetzt wichtig ist: 4 zentrale Treiber
Digitale Souveränität ist heute wichtiger denn je. Digitale Systeme sind für den Betrieb von Organisationen kritisch geworden. Gleichzeitig sind die Risiken rund um Kontrolle, Compliance und Kontinuität deutlich gestiegen.
Hier sind vier zentrale Gründe, warum digitale Souveränität heute eine geschäftliche Priorität ist und nicht nur ein technisches Thema.
1. Regulatorische und rechtliche Risiken nehmen zu
Der regulatorische Druck nimmt in vielen Regionen zu, besonders in Europa.
Rahmenwerke wie GDPR, NIS2 und DORA erhöhen die Anforderungen daran, wie Organisationen Daten, Sicherheit und operative Resilienz managen. Gleichzeitig werden rechtliche Konflikte zwischen Jurisdiktionen immer schwerer zu ignorieren.
Unter Gesetzen wie dem US CLOUD Act können US-Behörden US-basierte Cloud-Anbieter dazu verpflichten, Daten herauszugeben, unabhängig davon, wo diese Daten physisch gespeichert sind.
Für Organisationen in regulierten Umgebungen schafft das Unsicherheit bei Compliance und Kontrolle.
2. Die Kontrolle über digitale Systeme verlagert sich nach außen
Viele Organisationen gehen davon aus, dass sie ihre Systeme, Daten und Abläufe kontrollieren.
In der Praxis hat sich diese Kontrolle jedoch zunehmend nach außen verlagert zu externen Plattformen und Anbietern.
Das zeigt sich auf subtile, aber kritische Weise:
Der Speicherort der Daten ist festgelegt, unklar oder schwer nachzuweisen.
Die Infrastruktur wird außerhalb Ihrer Jurisdiktion und Kontrolle betrieben.
Das Systemverhalten wird von Anbietern statt von Ihren internen Teams definiert.
Mit der Zeit schränkt das Ihre Fähigkeit ein, Zugriffe zu steuern, Workflows anzupassen und auf Veränderungen zu reagieren.
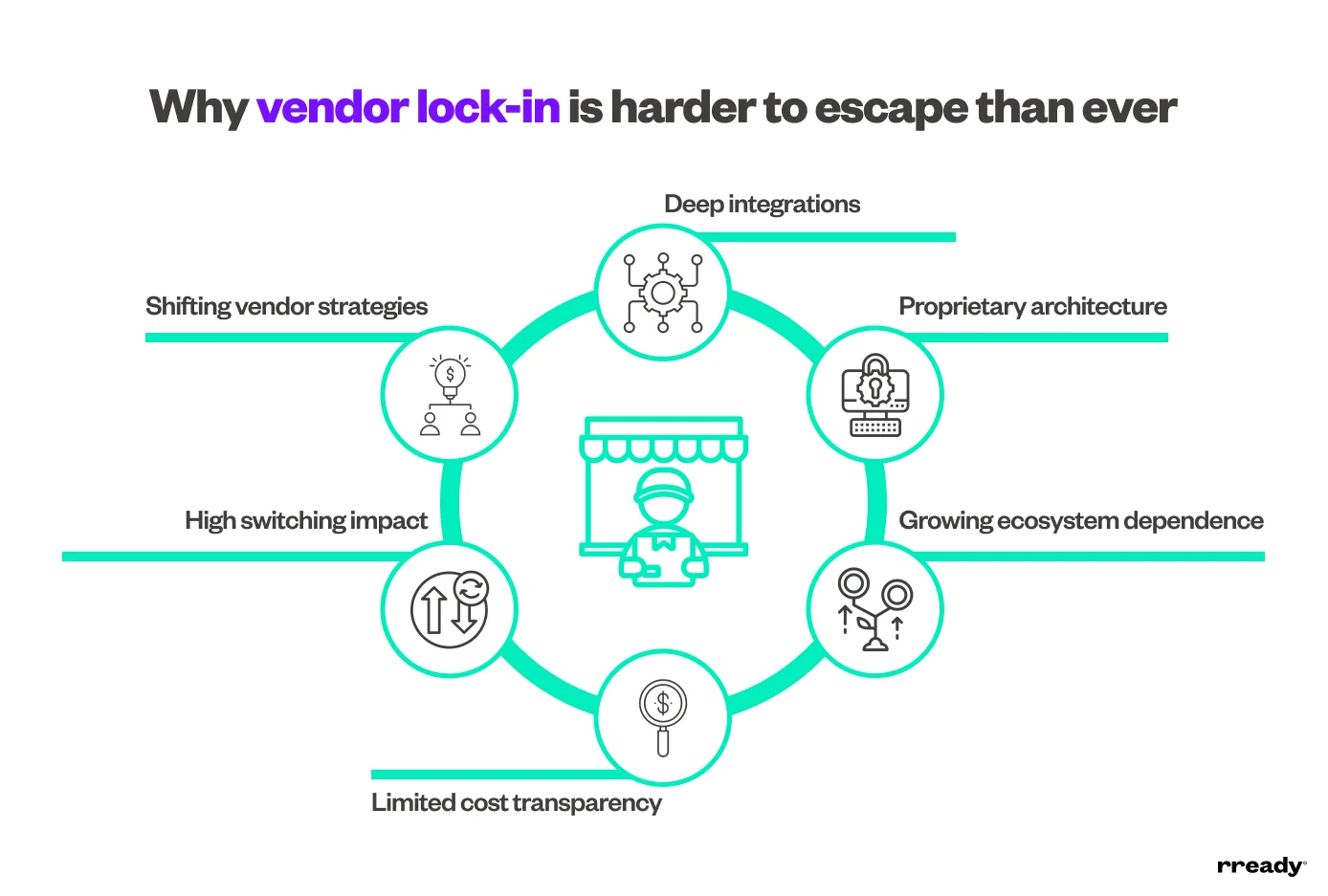
3. Vendor-Lock-in wird zum strategischen Risiko
Vendor-Lock-in war früher nur eine technische Einschränkung. Heute ist er ein Geschäftsrisiko.
Organisationen fällt es aus mehreren Gründen schwerer, sich von dominanten Plattformen zu lösen:
Integrationen sind tief eingebettet. Migrationen werden dadurch komplex und zeitaufwendig.
Architekturen beruhen auf proprietären Systemen, die die Interoperabilität einschränken.
Die Abhängigkeit von Anbieter-Ökosystemen wächst mit der Zeit weiter.
Preismodelle sind intransparent. Kostentreiber sind nur begrenzt sichtbar.
Ein Wechsel erfordert erheblichen Aufwand, birgt Risiken und stört den Betrieb.
Hinzu kommt, dass Anpassungen in der Anbieterstrategie Organisationen zwingen, ihre Pläne zu überdenken. Besonders, weil immer mehr Plattformen auf Cloud-first-Modelle umstellen.
4. Geopolitische und Cyberrisiken nehmen zu
Digitale Infrastruktur ist nicht mehr neutral. Sie wird von Geopolitik, Regulierung und globalem Wettbewerb geprägt.
Das zeigt sich in dem Anstieg der Cybervorfälle um 48 % im Jahr 2024, der teilweise durch wachsende geopolitische Spannungen getrieben wurde.
Gleichzeitig wachsen die Sorgen über die Abhängigkeit von ausländischen Technologieanbietern und die Konzentration von Macht bei wenigen Unternehmen.
Diese Risiken gehen über Sicherheit hinaus und betreffen die:
Geschäftskontinuität, besonders bei Störungen oder geopolitischer Instabilität
Operative Resilienz und die Fähigkeit, die Kontrolle über kritische Systeme zu behalten
Regulatorische Compliance über verschiedene Jurisdiktionen hinweg
Langfristige strategische Flexibilität und Unabhängigkeit
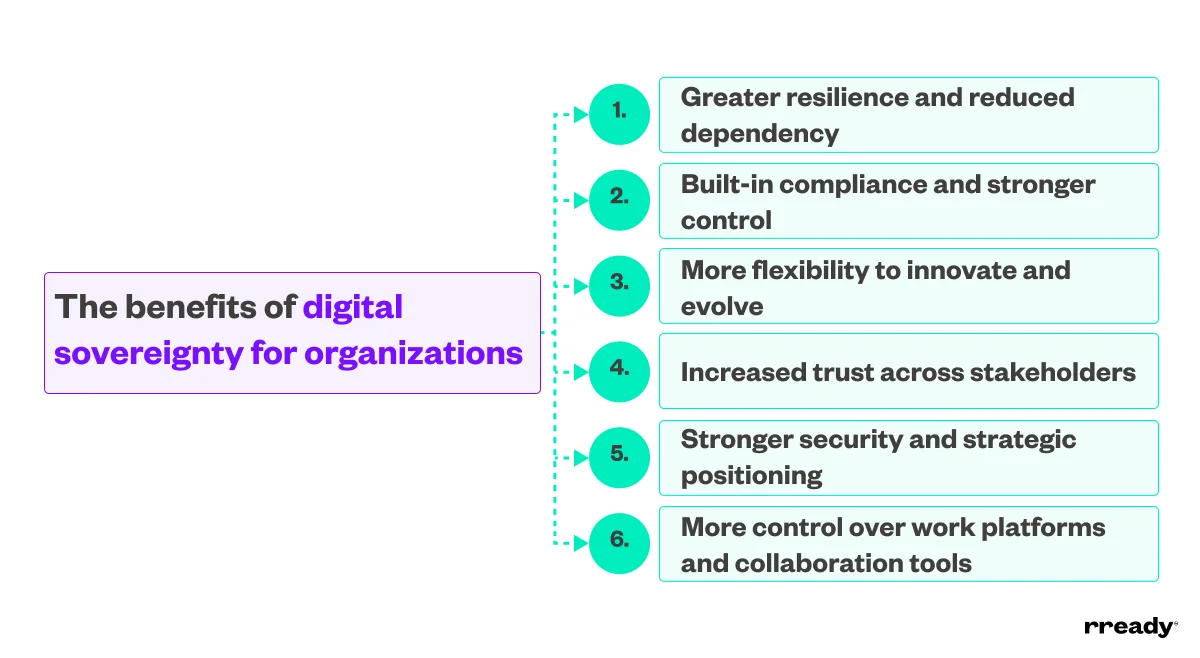
Warum der Weg zur digitalen Souveränität sinnvoll ist: 6 praktische Vorteile
Digitale Souveränität bringt Organisationen konkrete, messbare Vorteile. Sie gibt ihnen mehr Kontrolle über Systeme, Daten und die langfristige Ausrichtung. Das sind die sechs wichtigsten Vorteile:
1. Mehr Resilienz und weniger Abhängigkeit
Wer die Abhängigkeit von einem einzelnen Anbieter oder einem eng gekoppelten Ökosystem reduziert, verringert die Anfälligkeit für Störungen. Das stärkt die Geschäftskontinuität, weil Single Points of Failure wegfallen und Sie mehr Flexibilität bei Bereitstellung und Betrieb der Systeme erhalten.
2. Integrierte Compliance und stärkere Kontrolle
Wenn Sie festlegen, wo Daten gespeichert werden, wie sie verarbeitet werden und wer darauf zugreifen darf, wird Compliance Teil Ihrer Architektur. Das reduziert reaktive Korrekturen und erleichtert die Anpassung an neue Vorschriften.
3. Mehr Flexibilität für Innovation und Weiterentwicklung
Mit weniger Einschränkungen durch proprietäre Systeme können Sie neue Technologien einführen, etwa Cloud-native Plattformen und künstliche Intelligenz (KI), ohne die Kontrolle zu verlieren. So entsteht Raum, um zu experimentieren, zu iterieren und Ihre Systeme nach Ihren eigenen Vorgaben weiterzuentwickeln.
4. Mehr Vertrauen bei allen Stakeholdern
Klare Kontrolle über Daten und Systeme stärkt das Vertrauen von Kunden, Partnern und Regulierungsbehörden. Es zeigt, dass sensible Informationen verantwortungsvoll und nach den erwarteten Standards verarbeitet werden.
5. Stärkere Sicherheit und strategische Positionierung
Mit zunehmenden Cyberbedrohungen und geopolitischem Druck stärkt digitale Souveränität Ihre Fähigkeit, kritische Systeme zu schützen und in Krisen die Kontrolle zu behalten. Sie unterstützt langfristige Resilienz auf operativer und strategischer Ebene.
6. Mehr Kontrolle über Arbeitsplattformen und Kollaborationstools
Souveränität ist im Alltag besonders relevant. Wenn Arbeitsplattformen vollständig Ihrem Unternehmen gehören und von ihm kontrolliert werden, vermeiden Sie die Bindung von Wissen an proprietäre Systeme, reduzieren die Abhängigkeit von externen Ökosystemen und bewahren Flexibilität bei Teamzusammenarbeit und Skalierung.
So bewegen Sie sich in 5 strategischen Schritten in Richtung digitale Souveränität
Der Weg zur digitalen Souveränität ist keine einmalige Entscheidung. Es ist ein strukturierter Prozess, der die Kontrolle mit der Zeit aufbaut. Diese fünf Schritte helfen beim Einstieg:
Schritt 1: Ihre Abhängigkeiten erfassen
Die meisten Organisationen unterschätzen, von wie vielen externen Systemen ihre Abläufe abhängen.
Deshalb sollten Sie zuerst ein klares Bild davon erstellen, wovon Sie im Tagesgeschäft abhängig sind. Dabei hilft der Blick auf:
Welche Plattformen und Anbieter Sie nutzen
Welche Systeme Ihre Kern-Workflows unterstützen
Welche Tools schwer zu ersetzen oder zu migrieren sind
Schritt 2: Ihr Risikoprofil bewerten
Abhängigkeiten bringen oft Risiken mit sich, die nicht sofort sichtbar sind. Das gilt besonders für rechtliche Risiken, Compliance und operative Kontrolle.
Um Ihr Risikoprofil zu bewerten, sollte Ihre Organisation Folgendes prüfen:
Wo Ihre Daten gespeichert sind und welche Jurisdiktionen gelten
Wer unter welchen Bedingungen auf Ihre Systeme zugreifen kann
Welche Vorschriften und Compliance-Anforderungen Sie erfüllen müssen
Wie stark Sie für kritische Abläufe von externen Anbietern abhängen
Schritt 3: Kritische Systeme und Daten priorisieren
Nicht alles muss gleichzeitig verändert werden. Konzentrieren Sie sich auf die Bereiche mit der größten Wirkung und beginnen Sie mit:
Geschäftskritischen Tools und Workflows
Sensiblen oder regulierten Daten
Systemen mit hohen Wechselkosten
In vielen Organisationen sind Arbeitsplattformen und Kollaborationstools ein natürlicher Ausgangspunkt. Sie stehen im Zentrum des Tagesgeschäfts, speichern viel institutionelles Wissen und hängen oft stark von externen Anbietern ab.
Schritt 4: Souveräne Alternativen bewerten
Wenn Ihre Prioritäten feststehen, besteht der nächste Schritt darin, zu prüfen, wie gut verschiedene Lösungen digitale Souveränität in der Praxis unterstützen.
Konzentrieren Sie sich auf die Faktoren, die bestimmen, wie viel Kontrolle Sie über Ihre Systeme behalten:
Faktor | Worauf Sie achten sollten |
Datenkontrolle | Klare Kontrolle darüber, wo Daten gespeichert werden, wie sie verarbeitet werden und wer zugreifen kann |
Operative Kontrolle | Möglichkeit, Workflows, Systemverhalten und Zugriffe ohne vom Anbieter vorgegebene Einschränkungen zu definieren |
Jurisdiktionale Ausrichtung | Infrastruktur und Betrieb sind auf Ihre regulatorischen und rechtlichen Anforderungen abgestimmt |
Kostenklarheit | Planbare Preise mit transparenten Kostentreibern und ohne unerwartete Upgrades |
Flexibilität und Interoperabilität | Offene APIs, modulare Architektur und die Möglichkeit, sich in bestehende Systeme zu integrieren |
Kontrolle über die Systementwicklung | Freiheit, Systeme anzupassen, zu erweitern und weiterzuentwickeln, ohne an die Roadmaps des Anbieters gebunden zu sein |
Schritt 5: Klein anfangen und gezielt skalieren
Digitale Souveränität wird am besten Schritt für Schritt umgesetzt. Ein fokussierter Pilot hilft Ihnen, Annahmen zu testen, ohne die gesamte Organisation zu stören.
Starten Sie mit einem Team oder einer Abteilung, idealerweise in einem Bereich, in dem die Arbeit bereits über eine Plattform strukturiert wird, zum Beispiel:
Projektmanagement
Softwareentwicklung
Issue-Tracking
Servicebereitstellung
Interne Zusammenarbeit
Wissensmanagement
So können Sie Leistung, Kontrolle und Benutzerfreundlichkeit in einer realen Umgebung validieren.
Von dort aus können Sie schrittweise erweitern, basierend auf dem, was funktioniert.
Dieser Ansatz reduziert Risiken und schafft zugleich Vertrauen und Dynamik für eine breitere Einführung.
Starten Sie mit sovara in Richtung digitale Souveränität
Der Weg zur digitalen Souveränität ist nicht einfach. Er erfordert Änderungen an Architektur, Governance und langfristigem Systemmanagement.
Während dieses Prozesses stehen Organisationen oft vor:
Höheren Anfangsinvestitionen und mehr Planungsaufwand
Komplexeren Anforderungen an Systemdesign und Governance
Der Herausforderung, Kontrolle und Flexibilität auszubalancieren
Trotz dieser Herausforderungen ist die Richtung klar. Die Frage ist nicht, ob Sie sich in Richtung digitale Souveränität bewegen sollten, sondern wo Sie anfangen.
Für viele Organisationen ist der wirksamste Startpunkt dort, wo die eigentliche Arbeit stattfindet.
Im Alltag wird die Arbeit oft über Plattformen wie Jira und Confluence gesteuert. Dort werden Workflows, Dokumentation und Entscheidungen zentralisiert. Diese Plattformen sind jedoch nicht mit Blick auf Souveränität entwickelt worden. Deshalb sind sie nicht vereinbar mit strengen Anforderungen an Datenresidenz, Zugriffskontrolle und System-Governance.
Eine souveräne Alternative, entwickelt und gehostet in der EU, ist sovara.
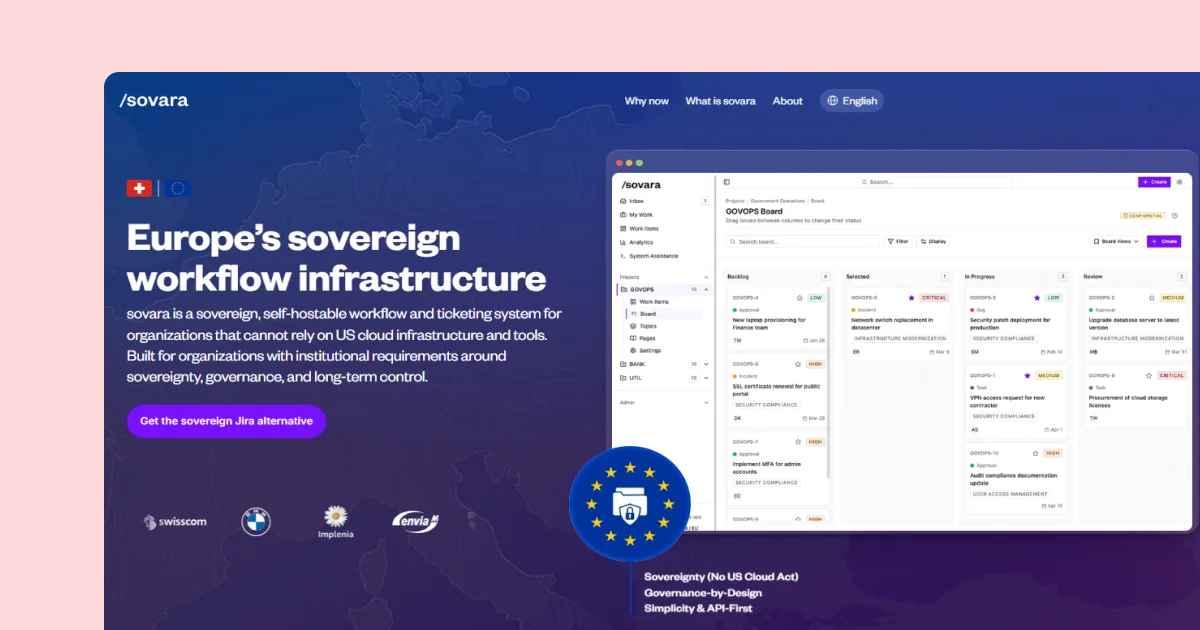
sovara ist eine souveräne Arbeitsplattform für Unternehmen und öffentliche Organisationen, die Kontrolle behalten wollen, ohne auf Flexibilität zu verzichten.
Sie adressiert die zentralen Herausforderungen digitaler Souveränität direkt:
Souveränität by Design: sovara stellt sicher, dass Daten in europäischen Jurisdiktionen gehostet und verwaltet werden, mit Optionen für souveräne Cloud und On-Premises-Betrieb.
Kontrolle über Daten und Betrieb: Eindeutige Kontrolle darüber, wo Daten gespeichert werden, wie auf sie zugegriffen wird und wie sich Workflows systemübergreifend verhalten.
Planbare und transparente Kosten: Die Preisstruktur ist auf langfristige Planung ausgelegt und bietet volle Transparenz über die Kostentreiber.
Moderne, interoperable Architektur: sovara ermöglicht die nahtlose Integration in bestehende Systeme über APIs und eine ereignisgesteuerte Architektur. So können Daten und Workflows kontrolliert bewegt werden.
Systementwicklung mit Zukunftssicherheit: Die KI-native Grundlage ermöglicht es Organisationen, den Einsatz von KI festzulegen. Dazu gehört die Option, eigene Modelle mitzubringen oder gehostete Modelle unter kontrollierten Bedingungen zu nutzen.
Sicherheit und Governance auf Enterprise-Niveau: sovara bietet strukturierten Zugriffsschutz, Nachvollziehbarkeit und Compliance-Unterstützung durch Funktionen wie SSO, GDPR-Ausrichtung und vollständige Audit-Logs.
sovara unterstützt auch die strukturierte Migration von bestehenden Plattformen. So können Sie kritische Workflows und Daten umstellen, ohne den Betrieb zu stören.
Buchen Sie eine Demo mit unserem Team, um den ersten Schritt in Richtung digitale Souveränität zu gehen und zu sehen, wie sovara in Ihre Umgebung passt.
